Test Altospam’s solutions!
Thousands of companies, CTOs, CIOs, CISOs and IT managers already trust us to protect their e-mail against phishing, spear phishing, ransomware, …
This article presents our recommendations for setting up the Altospam solution. It is not intended to replace the documentation, but to complement it by explaining specific options related to questions regularly received by Altospam support.
Whitelisting is a sensitive action. Indeed, messages from a whitelisted address or domain will no longer be subject to anti-spam checks. This also implies the absence of important checks:
– Control of the sending server, including SPF validation, sending IP reputation, message traversal with the various servers or routers used.
– Content verification, including DKIM validation, presence of dangerous links, suspicious Javascript code, etc.
– Analysis of attachments with zero-day vulnerability detection systems, macro control for Office documents to detect truly dangerous scripts, or the presence of executable elements in PDF documents.
Note that if an attacker impersonates a sender you’ve whitelisted, the message will be accepted, unchecked.
Nevertheless, it is sometimes necessary to override these protections for clearly identified messages from known and trusted senders. If you need to force reception of a message that doesn’t pass the checks, you have two options:
– Use the general whitelist. It is accessible from the administration interface and concerns all the domains of the associated account. The general whitelist takes into account both the envelope address (the technical sending address, the one displayed in Altospam’s logs) and the display address (the one displayed in your e-mail client). More details on these addresses in the following article: here
– Use your personal whitelist. It only concerns the mailbox in question. It can be accessed both from the administration interface and from the user interface. It only takes into account the envelope address, the technical sending address that appears in Altospam’s logs.
Using the personal list is more secure, as it restricts the scope of a possible attack from a listed address. On the same principle, always register a single address rather than a complete domain, to reduce the possibility of attack.
Bounces are automatic response messages. They are sent by a correspondent’s mail server when his mailbox is full, unreachable or in the case of an out-of-office message, for example. A more detailed definition can be found in the Altospam glossary: https: //www.altospam.com/en/glossary/bounce/
Some of these messages are relevant and provide useful information about the delivery of your messages. Others, on the other hand, are useless, or even risk flooding your inbox. For example, if an attacker impersonates you, from a server that has nothing to do with yours, it’s your address that will receive the bounces indicating the rejection of the messages sent. In this case, you run the risk of receiving a large number of messages in response to spam you didn’t send.
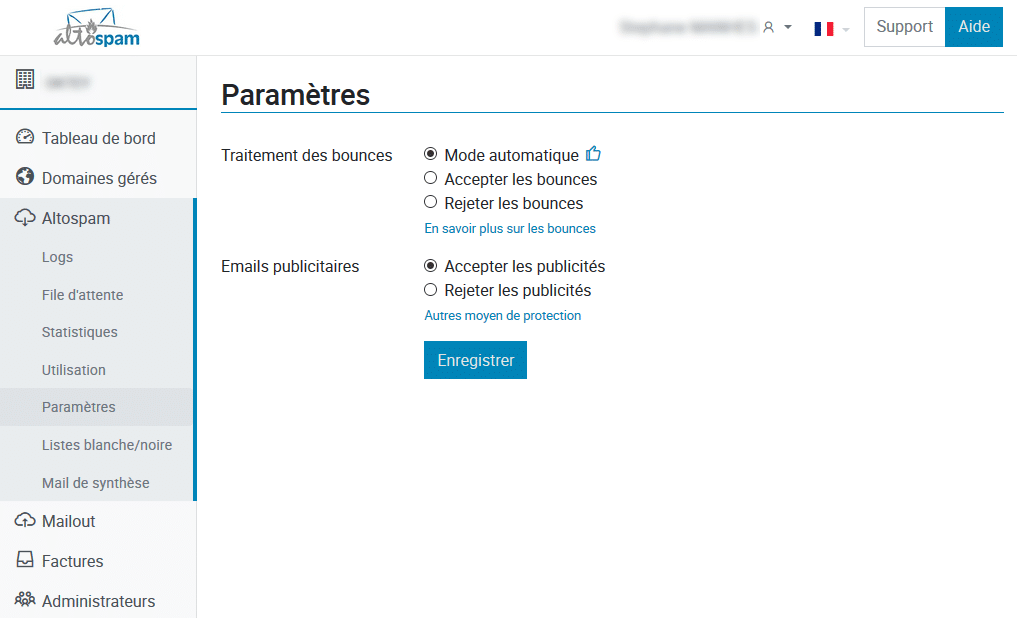
Altospam lets you control the flow of bounces. From the administration interface, you can set the level of regulation of this flow:
– Block all bounces,
– Accept all bounces,
– Trust Altospam (automatic mode).
This last choice is the default configuration and the one recommended in most cases. In this setting, our systems try to sort out the important bounces and block the others. Occasionally, an absence message may be stopped by this system, due to the content of the initial message or its excessive frequency, for example, but this mainly concerns common or even trivial messages.
This filter, deactivated by default on Altospam, is designed to block advertising as well as newsletters or mailing lists, all mass emails. These messages aren’t spam, they don’t hide their identity or present any threat, but they may be unwanted. Technically, the filter is based on the presence of certain headers (“Precedence: bulk”, for example), unsubscribe or account management links and the reputation of the sending servers, whether or not they are known for emailing, or “routers”.
You should therefore bear in mind that a newsletter subscription, even if intended and validated, will in most cases be blocked by this system if it is activated.
However, it is possible to fine-tune the ad filter by applying it only to certain addresses rather than to the entire domain. For example, you may wish to block such content on generic addresses (contact@exemple.fr, service@exemple.fr…) but allow it on personal addresses, or directly block ads only for a list of clearly identified addresses.
Another solution is to manage ads directly on the mail server. Altospam adds information to message headers when it detects a message affected by the ad filter, even if the filter is deactivated and the message forwarded. This is the “X-ALTOSPAM-STATUT” header, whose value is set to “bulk”. Find out more about this possibility in the dedicated article on our blog: here
All the settings for these different options are described in the documentation, details of which can be found in the Altospam administration interface by selecting the Help button in the top right-hand corner. And, of course, you can contact our support team by phone or e-mail for assistance with any questions you may have.
Test Altospam’s solutions!
Thousands of companies, CTOs, CIOs, CISOs and IT managers already trust us to protect their e-mail against phishing, spear phishing, ransomware, …