Securing domain names
Definition of DNSSEC
DNSSEC (Domain Name System Security Extensions) is a standardized protocol for securing DNS data. By default, this data is not encrypted, enabling an attacker to intercept or even modify a transaction, in particular to direct a user to a pirate server, without his or her knowledge. DNSSEC does not encrypt the connection, but signs the response using asymmetric cryptography, enabling the client to confirm its validity.
To achieve this, DNSSEC uses dedicated fields:
- DNSKEY: Contains the domain’s public key, enabling the client to validate the encrypted data. It corresponds to the private key used to generate RRSIGs.
- RRSIG: Contains the DNS data signature. The fields are grouped by name+type association (for example: example.fr TXT or example.fr MX), and are then referred to as RRset. A fingerprint is generated for each RRset, and they are then encrypted by the private key associated with the DNSKEY. There must therefore be as many RRSIGs as there are name+type associations.
- NSEC, NSEC3 and NSEC3PARAM: These contain proof of the non-existence of a domain or registration. NSEC3 and NSEC3PARAM, which appeared later, fulfill the same role, but do not provide a complete listing.
- DS, CDS and CDNSKEY: Contains a fingerprint of the DNSKEY public key associated with the domain name. DS has the particularity of being hosted by the parent zone of the domain being queried. For example, the DS record for “example.fr” is managed and hosted by the servers managing the “fr” zone. The purpose of this field is to create a chain of trust between affiliated zones, with the parent zone validating the key proposed by its child zone. In this way, we can confirm the validity of DNS responses all the way back to the root. CDS and CDNSKEY automate this process, allowing the parent to take into account any changes in the daughter zone’s DNSKEY.
Examples
The client workstation will ask its DNS resolver for the address of the mail servers managing the “example.fr” domain. The resolver, which is set to check for DNSSEC availability, queries the DNS chain to determine the domain’s authoritative server: ns1.example.fr (DNS tree explanations and demonstrations).
The MX request is then sent to the DNS server “ns.example.fr”, which replies :
- The MX fields (as it would without DNSSEC),
- The corresponding RRSIG field,
- The DNSKEY field, which decrypts the RRSIG field.
It also queries the DNS server of the parent zone, in this case “fr”, which responds with :
- The DS field, which validates that the DNSKEY is not forged.
With this information, the resolver can now :
- Validate the DNSKEY using the DS fingerprint,
- Decrypt the RRSIG using the DNSKEY fingerprint,
- Compare the decrypted RRSIG with the MX field supplied.
If everything is valid, the response is accepted. If the response has been modified by a “man-in-the-middle” attack, the RRSIG will not match the DNSKEY. If the DNS server is compromised or hacked, the DNSKEY would not match the DS fingerprint.
Why activate DNSSEC?
Activating DNSSEC in email security is also important to guarantee the authenticity and integrity of DNS resolutions used in email communication processes. Indeed, many stages of email transmission involve the use of domain names and DNS resolutions to verify sender authenticity, avoid phishing and prevent spam.
Without DNSSEC enabled, DNS resolutions can be falsified or manipulated, enabling attackers to redirect email traffic to malicious servers, carry out phishing attacks, propagate malware, or even block email delivery.
By enabling DNSSEC, domain owners can protect email communication processes against man-in-the-middle attacks, boost recipients’ confidence in received emails, and improve quality of service by avoiding disruptions due to attacks on DNS resolutions.
Applications
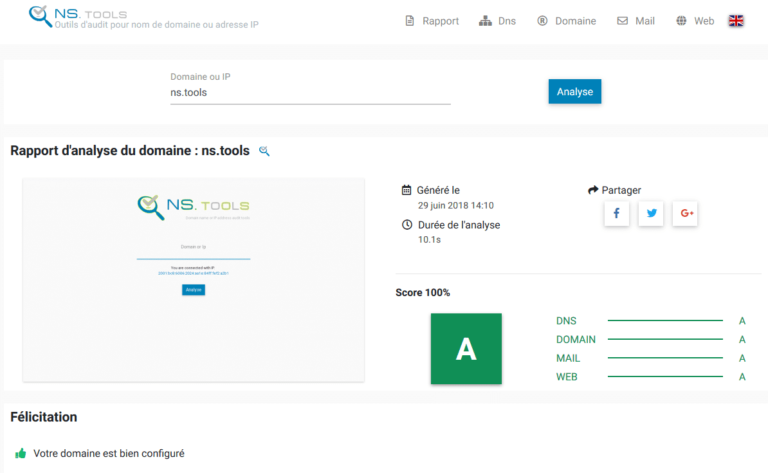
The “altospam.com” domain and all its sub-domains are protected by DNSSEC. So when a message is delivered to one of our customers, the name resolution of our servers is secured against any form of modification or usurpation.
Would you like to strengthen your email security?
Security starts in your mailbox. We offer a free 15-day e-mail analysis.